Cerco's Training Pathways
Cerco's long standing and well respected training provides valuable pathway options into IT.
Choose your pathway
Pathway 1 - Contract Work
Our 5-day, entry-level training course and subsequent contract work with the option of permanent employment.Pathway 2 - Cyber Security
For those with aspirations towards Cyber Security we extend our training to cover Cyber Security through our Cradle to Cyber® program.Through our partnership with the world leader in network security solutions, Fortinet, we are able to provide access to the full NSE (Network Security Expert) Training and Certification program.
Pathway 3 - Permanent Employment
You may wish to complete your FastTrack training and move straight into permanent employment. Our permanent recruitment team will work with you to secure your role.Cerco FastTrack Training

This course, as the name may suggest, is designed to quickly equip you with the core skills to become an IT Field Engineer.
To that end it is designed to meet the technical requirements outlined by our clients.
We will teach the basics of computer hardware, software and configuration in a practical, hands-on manner that prepares you for a range of duties including, but not limited to:
- Server / hardware maintenance
- Software configuration
- Network configuration
- Server / hardware installation and removal
- Printer installation

We also undertake contract specific training where candidates may be trained on-site or invited back to our training centre. This could be to cover things such as Retail EPOS installations through to mounting of Audio Visual equipment.
Once you have completed the course you will possess the necessary skills and knowledge for the effective support of networked PC systems and common peripherals, together with a sound foundation on which to build further product training.
The course includes assessments for Cerco's exclusive Cerco Certificate in Systems and Networking (CCSN), which is recognised by our employer partners as an entry-level qualification for systems service technicians.
Cerco FastTrack Training Detail
- Health and safety in the workplace
- Electrostatic discharge
- PC hardware connections
- PC data storage
- PC memory
- How to strip down a PC
- The ROM BIOS & CMOS set-up
- Scripted install of a Windows 10 image
- WDS install of Windows 10
- Windows 10 configuration
- Command line
- Network Basics
- Network Media
- Network Topology
- Network Standards Hubs, Switches and Routers
- Network access methods
- Windows Networking
- Network configuration
- Joining Windows domains
- Wireless networking
- TCP / IP Networking
- TCP/IP Overview
- TCP/IP Addressing
- Name resolution
- IP Address resolution
- Routing
- DHCP
- TCP/IP Connectivity
- TCP/IP
- Troubleshooting
- Logical fault finding/troubleshooting
- Printer installation in Windows
Soft Skills
- Customer care for IT support personnel
- Appearance, politeness and listening
- Handling complaints
No prior formal computer training is required but you must have awareness of, and some familiarity with PC hardware and the use of PC systems, and you must possess suitable aptitude and a full, clean driving licence.
Our permanent recruitment team are on hand at all times should you wish to discontinue contract work and seek permanent employment.
Please note that the course is FREE to attend but we do require an initial, one-off payment of £85 to cover the cost of Course Certification and a DBS Check .
Cradle to Cyber®
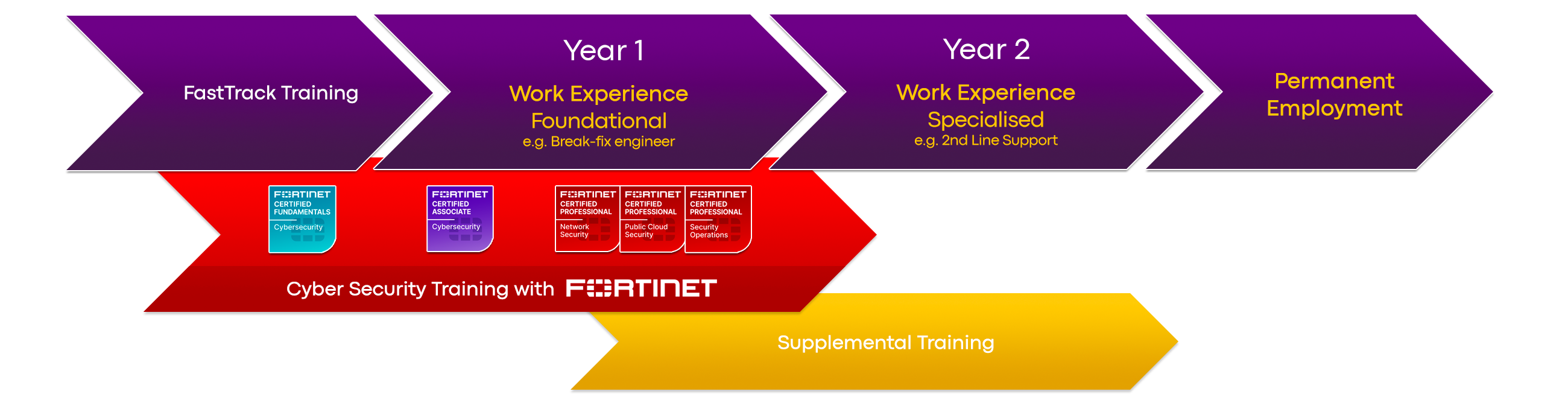
If you have aspirations toward a career in Cyber Security you can extend your training with our Cradle to Cyber programme.
Fortinet NSE Training and Certification
Through our partnership with Fortinet we are able to provide you with access to the Fortinet NSE Training and Certification Program, which forms the spine of our cyber security training.
The certifications that comprise the Fortinet Network Security Expert (NSE) program have been identified as ideal qualifications to gain work experience with our employment partners. Crucially, you are able to study while you work.
Cradle to Cyber will prepare you for your first role in the Cyber Security industry. The duration of the program is two years.
Supplemental Training
Additionally, and where relevant, we can also provide supplementary training for certifications from CompTIA, ITIL, ISACA and Microsoft.
The programme is designed to gain access to the following positions at entry level:
Read more about Cradle to Cyber
Cradle to Cyber is available at no cost to those who have trained through Cerco's FastTrack and subsequently worked for us.
Straight to Permanent Employment

Our employment partners are always looking for fresh talent and Cerco's FastTrack training has proven to be a valuable pre-requisite for obtaining an interview.
Our permanent recruitment team will work closely with you to identify your ideal role.